Alerts
- Alerts
- Predefined alerts
- Monitoring Docker: Collector Failed License Checks
- Monitoring Docker: Collector License Expiration (less than 14 days)
- Monitoring Docker: Collector license overuse
- Monitoring Docker: Collector outdated
- Monitoring Docker: Warning: container cpu is throttled
- Monitoring Docker: Warning: docker runtime disk space is low
- Monitoring Docker: Warning: high container memory usage
- Monitoring Docker: Warning: high host memory usage
- Monitoring Docker: Cluster Warning: high host CPU usage
- Monitoring Docker: Warning: collectord reports errors in one or more pipelines
- Monitoring Docker: Warning: collectord has WARN or ERROR logs
- Monitoring Docker: Warning: Increasing lag between event time and indexing time in container logs
- Monitoring Docker: Collectord diagnostics
- Alert triggers
- Links
- Predefined alerts
Predefined alerts
Available since version 5.2
Monitoring Docker application has predefined alerts, that help to monitor the health of your clusters and performance of containers.
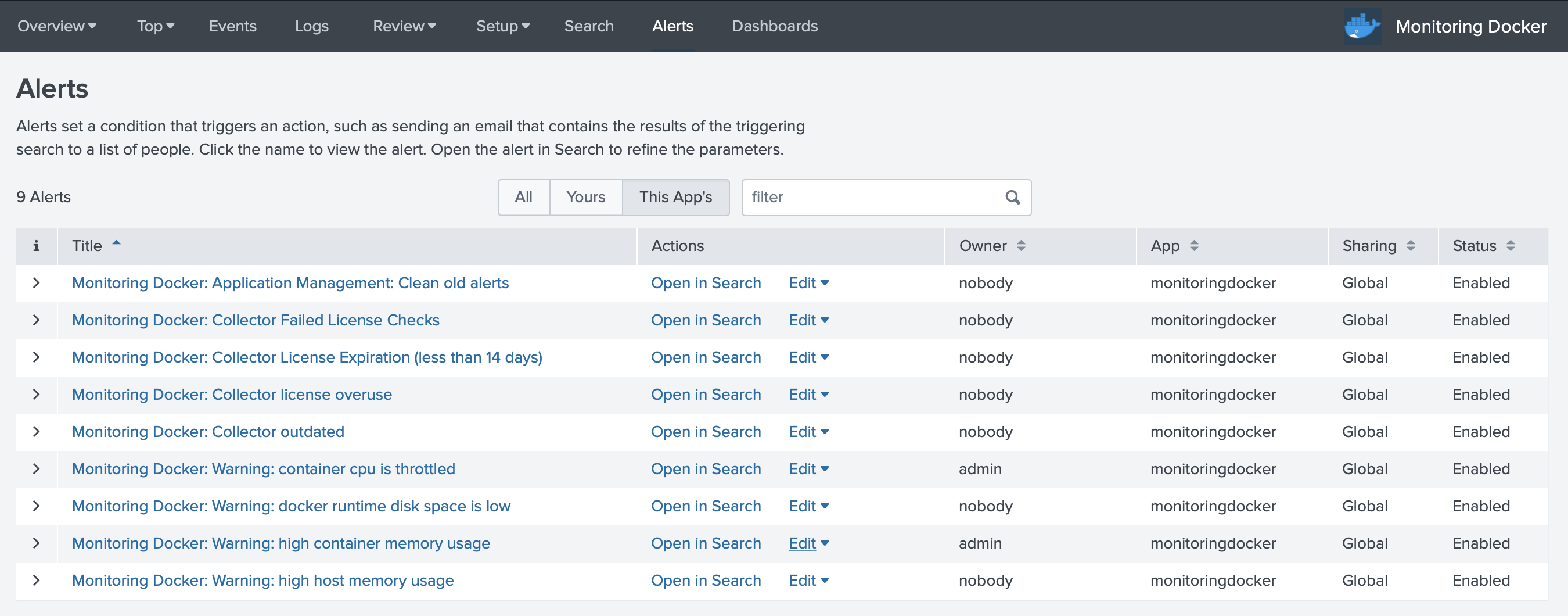
Monitoring Docker: Collector Failed License Checks
Notifies if collector failed to check the license with the licensing server.
Monitoring Docker: Collector License Expiration (less than 14 days)
Notifies about license expiration.
Monitoring Docker: Collector license overuse
Notifies if in the cluster application sees more collectors than allowed with the license.
Monitoring Docker: Collector outdated
Notifies if the collector running in the system are outdated comparing to the application.
Monitoring Docker: Warning: container cpu is throttled
Notifies if a container is getting throttled for more than 20% of CPU. Consider increasing the CPU limits.
Monitoring Docker: Warning: docker runtime disk space is low
Docker runtime has less than 20% of disk space.
Monitoring Docker: Warning: high container memory usage
The container uses more than 85% of the memory given by the limit.
Monitoring Docker: Warning: high host memory usage
Docker host uses more than 85% of the host memory.
Monitoring Docker: Cluster Warning: high host CPU usage
Docker host uses more than 90% of CPU on average for the last 5 minutes.
Monitoring Docker: Warning: collectord reports errors in one or more pipelines
Collectord reports errors in one or more pipelines
Monitoring Docker: Warning: collectord has WARN or ERROR logs
Collectord reports warnings or errors
Monitoring Docker: Warning: Increasing lag between event time and indexing time in container logs
Increasing lag between event time and indexing time in container logs
Monitoring Docker: Collectord diagnostics
Monitors Collectord logs and triggers when one or more ALARMs are ON, that getting triggered by diagnostics:: enabled in configuration.
Alert triggers
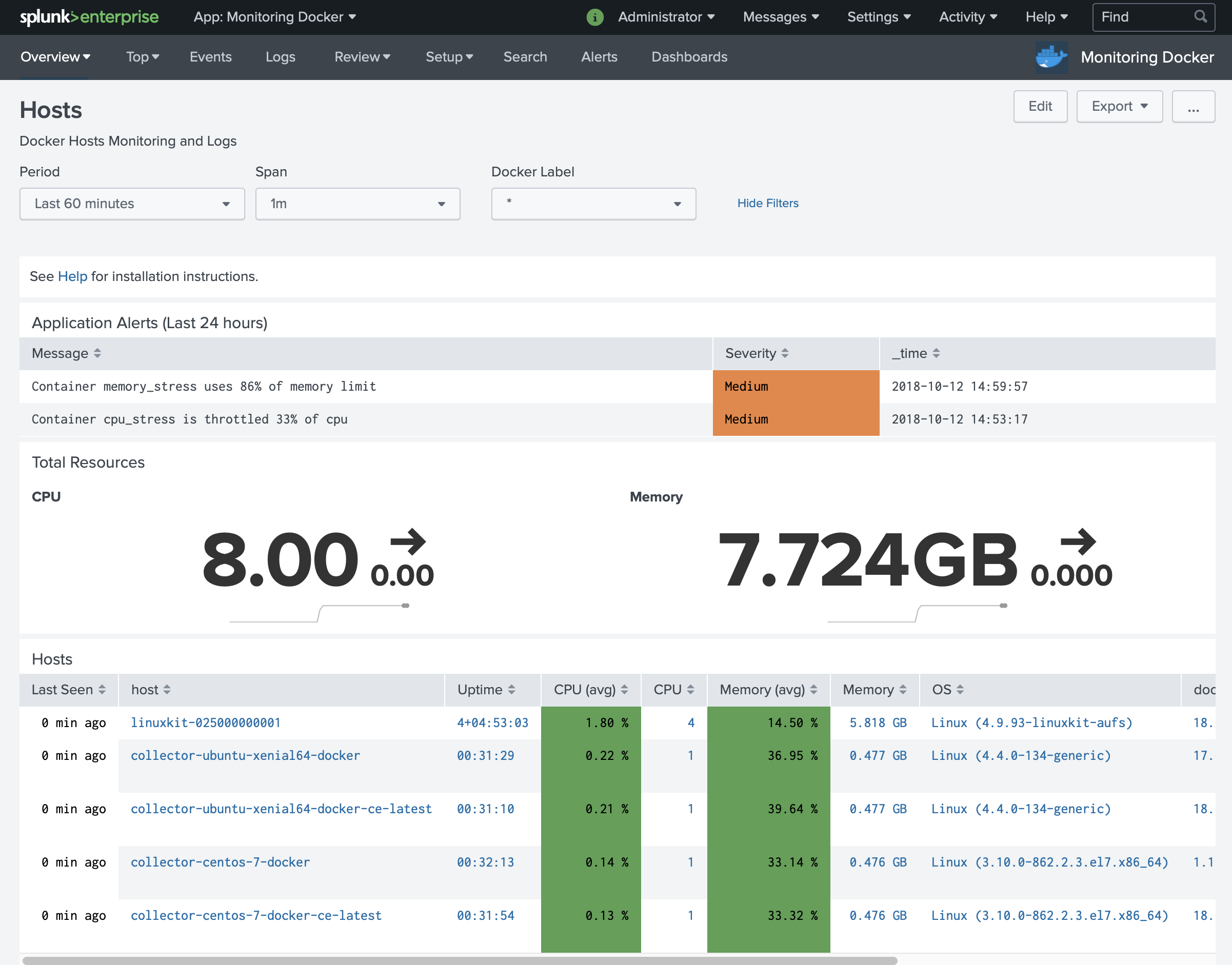
By default we show triggered alerts at the Hosts page at the very top. We populate this table using the rest call /alerts/fired_alerts/.
Other triggers
You can find various alerts actions on Splunk Base to integrate Splunk with the messaging applications and services for managing incidents.
After installing new alert action, you can modify existing alerts to add more triggers.
Links
-
Installation
- Start monitoring your docker environments in under 10 minutes.
- Automatically forward host, container and application logs.
- Test our solution with the embedded 30 days evaluation license.
-
Collector Configuration
- Collector configuration reference.
- Build custom image on top collector image with embedded configuration.
-
Container Annotations
- Forwarding application logs.
- Multi-line container logs.
- Fields extraction for application and container logs (including timestamp extractions).
- Hiding sensitive data, stripping terminal escape codes and colors.
-
Configuring Splunk Indexes
- Using not default HTTP Event Collector index.
- Configure the Splunk application to use not searchable by default indexes.
-
Splunk fields extraction for container logs
- Configure search-time fields extractions for container logs.
- Container logs source pattern.
-
Configurations for Splunk HTTP Event Collector
- Configure multiple HTTP Event Collector endpoints for Load Balancing and Fail-overs.
- Secure HTTP Event Collector endpoint.
- Configure the Proxy for HTTP Event Collector endpoint.
-
Collecting metrics from Prometheus format
- Configure collector to forward metrics from the services in Prometheus format.
-
Monitoring multiple clusters
- Learn how you can monitor multiple clusters.
- Learn how to set up ACL in Splunk.
-
Streaming Docker Objects from API Engine
- Learn how you can poll docker containers and images and forward them to Splunk.
-
License Server
- Learn how you can configure remote License URL for Collectord.
- Alerts
- Troubleshooting
- Release History
- Upgrade instructions
- Security
- FAQ and the common questions
- License agreement
- Pricing
- Contact



